Contact Trace Explorer combines a specialized tracing tool with a guided verification process to map pathways, quantify flows, and reveal gaps in contact tracing. The 888-884-4896 support line offers structured guidance for verified callers, emphasizing data-backed routing and auditable metrics. Workflows prioritize privacy, data minimization, and cross-source corroboration. The approach aims for reproducible results and standardized reporting, ensuring accountability. The implication is clear: a precise, transparent framework that invites scrutiny and sustained examination.
What Is Contact Trace Explorer and Why It Matters
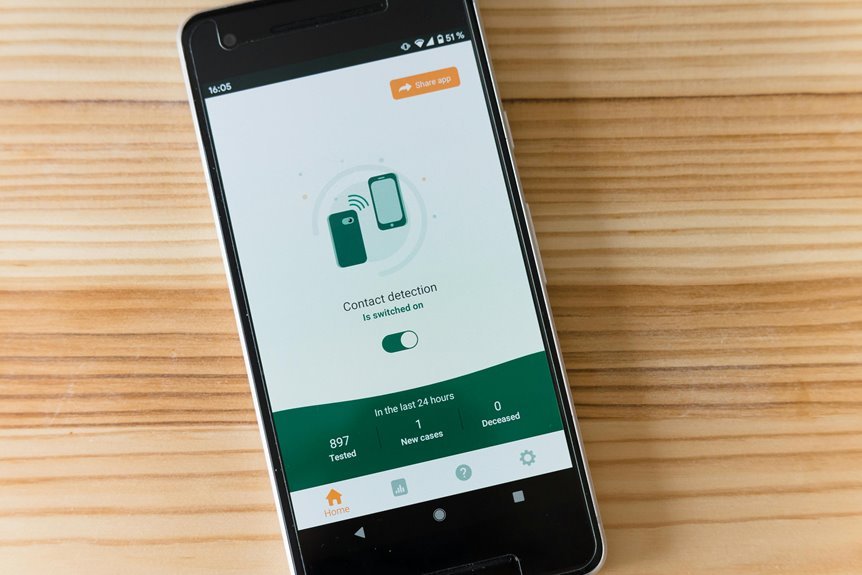
Contact Trace Explorer is a specialized tool designed to map and analyze the pathways of contact tracing within public health or security contexts. The system quantifies flows, prioritizes data integrity, and reveals gaps in processes. It supports decision makers with empirical insights on contact tracing and caller guidance, enhancing rapid response, accountability, and transparent operational effectiveness under varying surveillance requirements.
How 888-884-4896 Guides Verified Callers Through Tracing
The process by which 888-884-4896 guides verified callers through tracing is grounded in standardized verification steps and data-backed routing. Analysts present a data-driven framework that maps call origins to verified identifiers, minimizing false positives. 2 word discussion ideas emerge from methodical evaluation, emphasizing precision and transparency. Subtopic relevance hinges on reproducible metrics, audit trails, and cross-source corroboration for credible tracing outcomes.
Streamlined Workflows for Fast, Privacy-Conscious Investigations
Streamlined workflows enable rapid, privacy-conscious investigations by aligning data intake, verification, and case escalation with minimal manual handoffs. This approach emphasizes traceable, reproducible steps, data minimization, and auditability.
Privacy minded protocols reduce exposure while preserving speed. Investigation workflows integrate threat intelligence, verification metrics, and outcome logging, supporting scalable, independent decision-making without excessive oversight or redundancy.
Best Practices for Actionable Reporting and Compliance
Actionable reporting and compliance hinge on structured, evidence-based processes that translate investigations into clear, auditable outputs. The approach emphasizes reproducible methods, standardized templates, and transparent data lineage, enabling independent verification.
Data quality metrics guide evaluation, while privacy guidelines and verification processes ensure lawful handling, minimization, and timely disclosure to stakeholders without compromising operational flexibility or investigative autonomy.
Continuous improvement reinforces accountability and trust.
Conclusion
In the field, Contact Trace Explorer stands as a lattice of light—threads of data converge, gaps reveal themselves, and pathways map like a city grid at dawn. The 888-884-4896 guide acts as a steady compass, aligning verified callers with verifiable routes. Metrics punctuate the narrative, audits seal accountability, and privacy constraints trim the noise. The result is a crystalline workflow: precise, reproducible, and transparent, where actionable insights glow through minimized data, illuminating each investigative corridor.